Groundhog Day: Predicting Early Spring with PHP
In the quaint town of Punxsutawney, Pennsylvania, a unique tradition unfolds each year on February 2nd, known as Groundhog Day....
Understanding Man-in-the-Middle Attacks
Man-in-the-middle (MitM) attacks have earned a notorious reputation as one of the most insidious and potentially devastating cybersecurity threats today....
Creating a Command-Line Python Radio Player
In this tutorial, I'll walk you through the process of creating a command-line radio player using Python and ffplay, a...
Malware Detection with Maldet
Malware, short for malicious software, is a ubiquitous threat to all computer systems. It's the covert intruder that sneaks into...
Understanding and Implementing ClamAV on Linux
The perpetual arms race between threat actors and defenders often hinges on the tools each employs. For Linux users, one...
Simplifying SMS Alerts with Python and SMTP
Whether it's for emergency notifications or simple reminders, sending SMS alerts is a powerful way to get your message across....
Privacy-Focused Analytics: Balancing Insights and Integrity
Businesses of all sizes rely on data analytics to drive decisions, refine marketing strategies, and understand their audiences. Traditional web...
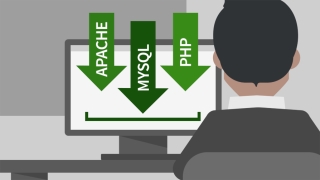
Automating JavaScript Minification with PHP
Automating JavaScript minification with PHP can significantly streamline a developer's workflow. It ensures that the deployed code is always in...
Secure Password Hashing with PHP
As a Software Engineer, I'm often confronted with the necessity of safeguarding users' sensitive information. One important aspect of user...
Converting Various Audio File Formats to MP3 Using Python
Audio files come in a variety of formats, such as WAV, FLAC, AAC, and OGG. However, MP3 remains one of...
Floorp Browser Review
The Floorp browser, a fork of the popular Firefox browser, has rapidly gained attention for its focus on privacy, customization,...
Calculating the Date of Easter Using the Computus Algorithm
Easter is one of the oldest and most significant festivals in the Christian calendar, celebrating the resurrection of Jesus Christ....
Merge Video Files with Python
Capturing memories or creating content often involves using devices like camcorders or smartphones. However, when recording long videos, users frequently...
Groundhog Day: Predicting Early Spring with PHP
In the quaint town of Punxsutawney, Pennsylvania, a unique tradition unfolds each year on February 2nd, known as Groundhog Day....
Understanding Man-in-the-Middle Attacks
Man-in-the-middle (MitM) attacks have earned a notorious reputation as one of the most insidious and potentially devastating cybersecurity threats today....
Creating a Command-Line Python Radio Player
In this tutorial, I'll walk you through the process of creating a command-line radio player using Python and ffplay, a...
Malware Detection with Maldet
Malware, short for malicious software, is a ubiquitous threat to all computer systems. It's the covert intruder that sneaks into...
Understanding and Implementing ClamAV on Linux
The perpetual arms race between threat actors and defenders often hinges on the tools each employs. For Linux users, one...
Simplifying SMS Alerts with Python and SMTP
Whether it's for emergency notifications or simple reminders, sending SMS alerts is a powerful way to get your message across....
Privacy-Focused Analytics: Balancing Insights and Integrity
Businesses of all sizes rely on data analytics to drive decisions, refine marketing strategies, and understand their audiences. Traditional web...
Automating JavaScript Minification with PHP
Automating JavaScript minification with PHP can significantly streamline a developer's workflow. It ensures that the deployed code is always in...